Introduction
The Trezor login process is an essential part of protecting your cryptocurrency and ensuring that only you can access your digital assets. Unlike traditional login systems that rely on passwords stored online, Trezor uses a hardware-based method designed to eliminate digital vulnerabilities. Through physical interaction with the device and secure offline storage of private keys, the login process provides a highly effective barrier against unauthorized access.
As cryptocurrency adoption increases, the importance of safe wallet access becomes even more significant. Trezor is built around the idea that your private keys should stay offline at all times. Understanding how to log in properly helps you stay in full control of your wallet while maintaining strong security practices.
The Purpose Behind Trezor Login
The goal of the Trezor login process is to authenticate the wallet owner without exposing sensitive data. Instead of connecting to online databases or storing passwords on servers, Trezor ensures that every layer of authentication happens on the hardware wallet and Trezor Suite. This prevents hackers from obtaining access through data breaches, phishing, or remote malware.
By eliminating online credentials entirely, Trezor reduces the risk of identity theft and password leaks. Your wallet can only be accessed when the physical device is connected and the correct PIN or passphrase is entered.
How the Login Process Works
Logging in begins the moment you connect your Trezor Model One or Model T to your device. Trezor Suite automatically detects the hardware wallet and requests authentication. This involves entering a PIN on a secure interface that prevents the computer from reading or tracking your input.
The device displays a randomized grid for PIN entry, ensuring that keyloggers or screen-recording malware cannot capture your PIN. This unique login method makes it extremely difficult for attackers to guess or intercept your credentials, even if they have access to your computer.
The Importance of PIN Security
Your Trezor PIN is the first layer of protection for your wallet. It ensures that even if someone physically obtains your device, they cannot access your crypto without entering the correct PIN. After several incorrect attempts, the device introduces increasing delays and may eventually wipe itself to prevent brute-force attacks.
Because the PIN is never entered directly onto your keyboard, it maintains a high level of security. Users should choose a PIN that is easy to remember but difficult for others to guess.
Using a Passphrase for Added Protection
Trezor also offers an optional passphrase feature. This passphrase functions as an extra layer of security that creates a hidden wallet accessible only with the correct phrase. Unlike the recovery seed, which must never be shared, your passphrase is something only you know and type in when needed.
Because the passphrase is not stored anywhere on the device, it provides strong protection even if your hardware wallet is lost or stolen. Each unique passphrase creates an entirely separate wallet, which helps users organize funds or add an additional privacy measure.
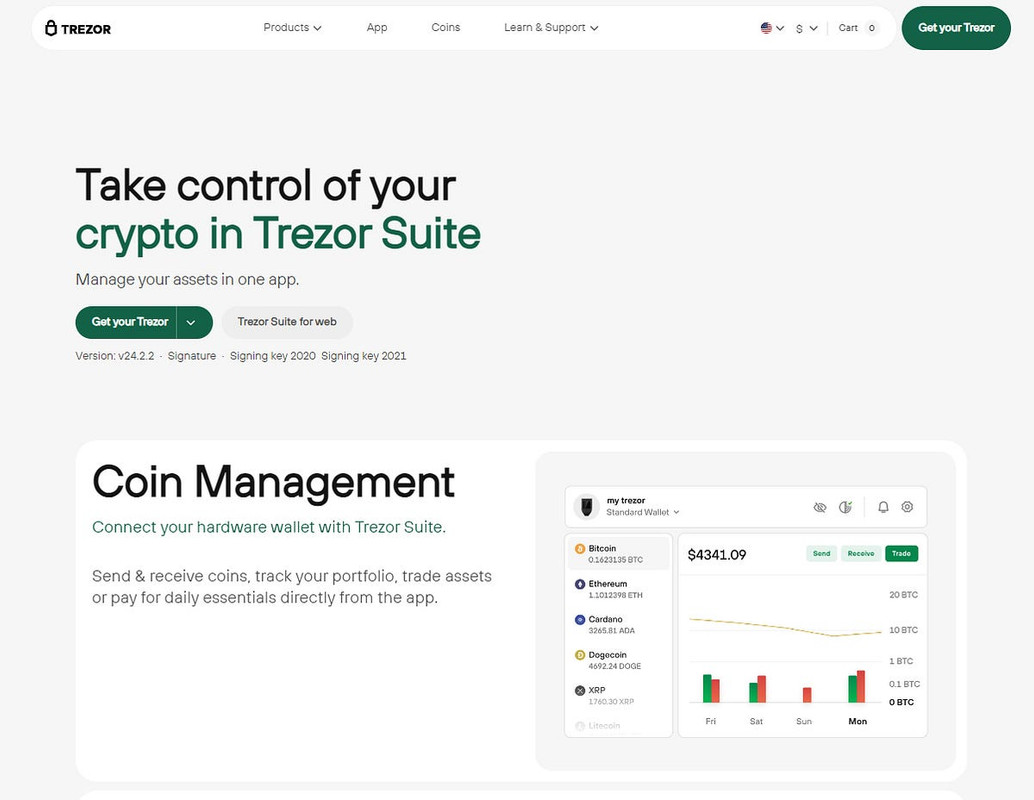
Accessing Crypto Through Trezor Suite
Trezor Suite is the official application that serves as the gateway to your crypto management tools. Once logged in through your hardware wallet, the Suite allows you to view balances, send and receive transactions, check price charts, install apps for supported coins, and manage portfolio settings.
The application is available for Windows, macOS, Linux, and through a secure web-based version. The desktop version is recommended for those wanting the highest level of security, as it minimizes susceptibility to browser-related risks.
Steps to Complete a Trezor Login
The login procedure is quick and straightforward:
- Connect your Trezor hardware wallet using the USB cable.
- Open Trezor Suite on your computer or use the web version.
- Allow the Suite to detect your device automatically.
- Enter your PIN using the secure Trezor login interface.
- Enter your passphrase if you choose to use one.
- Access your dashboard and begin managing your funds.
Every action during this process involves user confirmation, ensuring that no operation occurs without your approval.
Security Advantages of Trezor Login
Trezor’s login system provides several important advantages:
- No cloud credentials: Nothing stored online can be hacked.
- Offline verification: Sensitive data remains isolated from the internet.
- Physical confirmation: Each action must be approved on the device.
- Hardware-level protection: Private keys never leave the wallet.
- PIN and passphrase options: Multiple layers of authentication.
- Resistant to phishing: No login links or passwords to steal.
Best Practices for Safe Use
To keep your wallet secure, always download Trezor Suite from the official website. Keep your device firmware updated and never enter your recovery seed into any website, computer, or smartphone. Store your recovery phrase in a safe physical location, and consider enabling a passphrase for increased privacy.
Avoid connecting your Trezor device to public or untrusted computers, and always check transaction details on your device screen before confirming.
Conclusion
The Trezor login process is designed to give users complete control over their digital assets while maintaining advanced security protections. By combining secure PIN entry, offline verification, and physical device interaction, Trezor greatly reduces the risk of unauthorized access. Whether you are new to cryptocurrency or have years of experience, the Trezor login system ensures that your assets remain safe and accessible only to you.